According to reports, governments around the world are tightening control over citizens’ data and using claims of “fake news” to suppress dissent, eroding trust in the internet as well as the foundations of democracy.
Most government regimes and other organizations use the following ways to put internet injustices on individuals. They include Obstacles to access – majorly infrastructure barriers and total control of the internet, Limits on content – what’s is allowed and what’s not and lastly, violation of human rights – involves privacy and surveillance. All these are a total violation of Article 19 of the Universal Declaration of Human Rights.
“人人有權享有見解和言論自由;這項權利包括不受干涉地持有意見的自由,以及通過任何媒體尋求、接受和傳遞資訊和思想的自由,無論國界如何。
但在某些地方,情況更糟,因為除了上述不公正之外,公民可能會經歷互聯網關閉。
 互聯網關閉 – 其後果
互聯網關閉 – 其後果
Internet shutdown is the intentional disruption of the internet with the aim of making it unusable and inaccessible to exert control on the flow of information. It also involves the disruption of mobile apps and other electronic communication that may or may not rely on the internet. The government orchestrates internet shutdowns.
The most affected form of communication by government internet shutdowns is social media (Facebook, YouTube, Google, Blogs) and to an extent media houses. Internet shutdowns maybe total or partial especially in election times.
These injustices are majorly experienced in Asia and Africa. Some parts of Europe and South America are affected too. According to reports, these shutdowns have been on the rise and 2018 has a larger number of internet shutdowns than the previous years.
Internet shutdowns have various consequences such as diminished digital freedom of internet users and restraints on the growth of the economy.
在互聯網關閉和其他不公正中倖存下來
Most internet shutdowns are partial, and the involved agencies use techniques such as blocking of websites, censorship, and technical filtering of IP and inspections of data packets. Good news, these methods can be bypassed, and you can reclaim your digital freedom easily. Here is how;
- 使用信譽良好的 VPN
Reputable VPNs have strong encryption protocols that ensure your internet traffic is not visible to prying eyes including the government. These VPNs also implement Tor over VPN functionality to give you ultimate privacy when surfing the restricted internet. Most importantly, these VPNs use obfuscation techniques that scramble your VPN traffic and make it seem like normal traffic. This way, you get to avoid detection by government watchdogs and other regulating agencies.
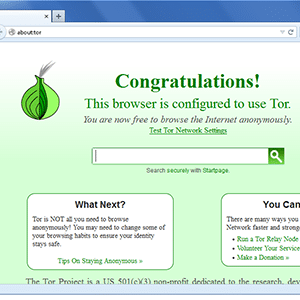
- 使用匿名工具,如 Tor
- 使用安全通信應用
Use untraceable communication apps that also offer end to end encryptions. Essentially, besides the above two ways, these apps will be very crucial in relaying information over a partial internet shutdown. One of the best apps to use is Signal.

 互聯網關閉 – 其後果
互聯網關閉 – 其後果

